Search results for "threat actors"
-

 3.0KMalware
3.0KMalwareBianLian Threat Actors Exploiting JetBrains TeamCity Flaws in Ransomware Attacks
The threat actors behind the BianLian ransomware have been observed exploiting security flaws in JetBrains TeamCity software to conduct their extortion-only attacks....
-

 2.8KData Breach
2.8KData BreachOkta’s Support System Breach Exposes Customer Data to Unidentified Threat Actors
Identity services provider Okta on Friday disclosed a new security incident that allowed unidentified threat actors to leverage stolen credentials to access...
-

 4.0KVulnerabilities
4.0KVulnerabilitiesGoogle TAG Detects State-Backed Threat Actors Exploiting WinRAR Flaw
A number of state-back threat actors from Russia and China have been observed exploiting a recent security flaw in the WinRAR archiver...
-
 3.0KMalware
3.0KMalwareQakBot Threat Actors Still in Action, Using Ransom Knight and Remcos RAT in Latest Attacks
Despite the disruption to its infrastructure, the threat actors behind the QakBot malware have been linked to an ongoing phishing campaign since...
-
 620Cyber Attack
620Cyber AttackThreat Actors Targeting Microsoft SQL Servers to Deploy FreeWorld Ransomware
Threat actors are exploiting poorly secured Microsoft SQL (MS SQL) servers to deliver Cobalt Strike and a ransomware strain called FreeWorld. Cybersecurity...
-

 446Ransomware
446RansomwareThreat Actors English-Speaking Countries with Customized Yashma Ransomware
An unidentified threat actor has deployed the Yashma ransomware variant since June 4, 2023, actively targeting English-speaking countries like:- Bulgaria China Vietnam...
-

 4.7KMalware
4.7KMalwareNew Analysis Reveals Raspberry Robin Can be Repurposed by Other Threat Actors
A new analysis of Raspberry Robin’s attack infrastructure has revealed that it’s possible for other threat actors to repurpose the infections for...
-
 1.5KData Security
1.5KData SecurityDon’t open emails from Microsoft Dynamics 365. Threat actors are exploiting its flaws to send phishing emails with legitimate Microsoft links
Microsoft’s Dynamics 365 Customer Voice is a software that is primarily used to collect customer feedback.It may be utilized to gather data...
-
 1.4KVulnerabilities
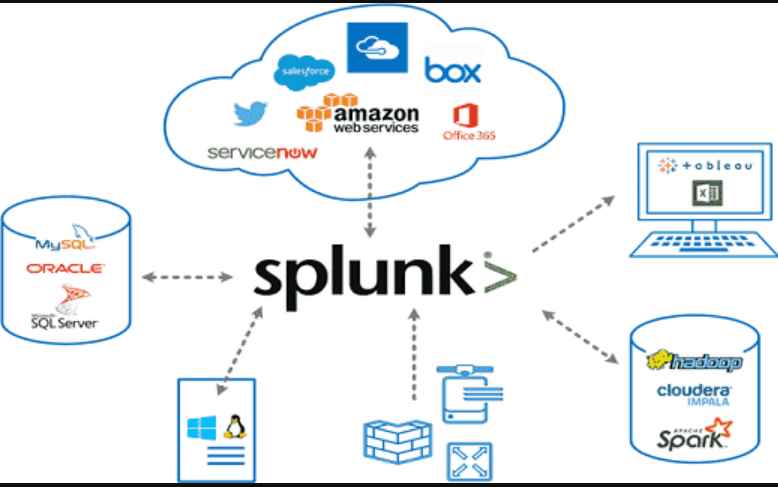
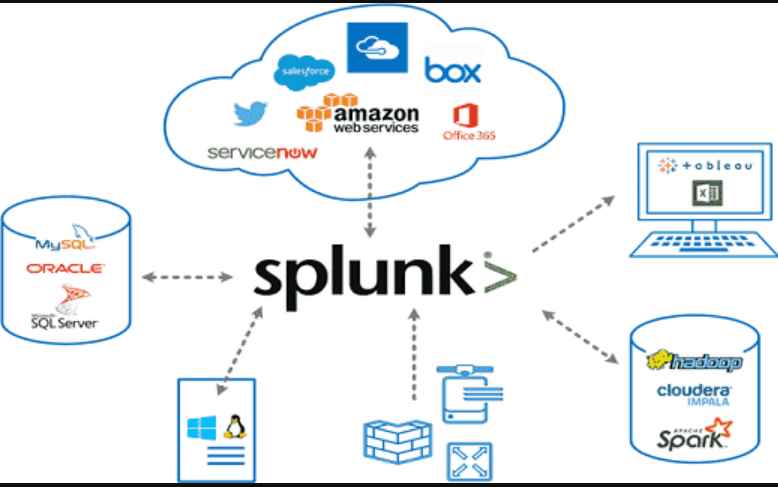
1.4KVulnerabilitiesEight high-severity vulnerabilities in Splunk Enterprise Software allow threat actors to take control of a network
With the use of the Splunk software, real-time data can be collected, indexed, and corroborated in a searchable repository from which graphs,...
-

 4.5KData Security
4.5KData SecurityHow Chinese threat actors are using recently discovered zero day flaws in office and Sophos firewall
By deploying a new Trojan named LOWZERO, integrated into an espionage campaign aimed against Tibetan organizations, the Chinese APT known as TA413...
-

 796Vulnerabilities
796Vulnerabilities60 different HP printer models of inkjet, LaserJet Pro, and PageWide Pro printers allow threat actors to take control of network remotely. Patch these two flaws
Two crucial flaws in the firmware of several corporate printer models have been made public by Hewlett Packard. If exploited, these flaws...
-

 2.1KVulnerabilities
2.1KVulnerabilitiesVulenerblity in UnRAR affects Linux & Unix Servers is being actively exploited by threat actors
The Cyber Security Agency of the United States (CISA) added to its catalog of vulnerabilities that are being actively exploited a recently...
-

 2.4KCyber Attack
2.4KCyber AttackThe Business of Hackers-for-Hire Threat Actors
Today’s web has made hackers’ tasks remarkably easy. For the most part, hackers don’t even have to hide in the dark recesses...
-
 3.1KVulnerabilities
3.1KVulnerabilitiesCritical OpenSSL vulnerability CVE-2022-2274 allows threat actors to remotely run code on your servers and encrypt them
OpenSSL is a famous cryptography library that provides an open source implementation of the Secure Sockets Layer (SSL) and Transport Layer Security...
-

 2.8KIncidents
2.8KIncidentsThreat actors could have hacked the U.S. Drug Enforcement Administration (DEA) and other related law enforcement agencies. Investigation still ongoing
The U.S. Drug Enforcement Administration (DEA) reports that it has begun an investigation into alleged cyberattacks that would have compromised up to...
-

 2.4KVulnerabilities
2.4KVulnerabilitiesThreat actors are exploiting critical vulnerability in F5 products to destroy firewalls and network devices completely
Cybercriminal groups have been exploiting a critical vulnerability in F5 BIG-IP solutions to erase file systems on affected devices, rendering servers completely...
-

 2.2KVulnerabilities
2.2KVulnerabilitiesThreat actors are actively exploiting a critical vulnerability, CVE-2021-20038, in SonicWall Secure Mobile Access (SMA) gateways. Update immediately
Cybersecurity specialists report that hacking groups are actively exploiting CVE-2021-20038, a severe vulnerability in SonicWall Secure Mobile Access (SMA) gateways, fixed in...
-

 4.2KIncidents
4.2KIncidentsThreat actors penetrate Australian Sunwater water supply systems
One of Australia leading water supply platforms confirmed that its systems were compromised by threat actors for nine long months. Apparently, threat...
-
 3.6KMalware
3.6KMalwareThreat Actors Using Squirrelwaffle Loader to Deploy Qakbot & Cobalt Strike Malware
A new threat emerged recently in the wild that drops malware like Qakbot and Cobalt Strike onto negotiated systems and networks; this...
-

 3.3KData Security
3.3KData SecurityTA544 threat actors hit Italian firms with Ursnif banking trojan
The IT security researchers at Proofpoint have discovered a new malware campaign in which threat actors from a group called TA544 are...
-

 4.3KCyber Crime
4.3KCyber CrimeThreat actors using CAPTCHA to evade phishing, malware detection
According to researchers, cybercriminals are abusing legitimate challenge and response services like Google’s reCAPTCHA or deploying customized fake CAPTCHA-like validation. Palo Alto...






